Just as new technologies are changing the workplace, new technologies and methodologies are also advancing among cybercriminals. The recent attacks at Target, Neiman Marcus and others utilized a combination of highly-sophisticated attacks that incorporated social engineering, parsing malware, and more. More and more businesses face the threat of advanced attacks like longline phishing.
Proofpoint coined the term “longline phishing” after the commercial fishing technique known as “longling.”[1] Classic phishing attacks attempt to get usernames, passwords and/or other vital information by tricking recipients into thinking that the request has come from a reliable source. Phishing attacks typically come through email, text messages and even social messaging. The recipient may recognize the source as a colleague, friend, or business (like a bank).
In recent years, companies have used security tools that can help flag and block potential phishing attacks, thus reducing the likelihood of success. Advancing phishing techniques evolved to bypass security protocols, but these attacks required highly customized messages that limited the email volume to a specific organization. So the cost/benefit of phishing attacks limited large scale attacks.
Enter longline phishing. Now cybercriminals have developed a technique for large-scale email attacks that appear to be customized emails and tend to pass by traditional security barriers. To top it off, they have high click-through rates, making them a lucrative tool for collecting vital data. “Many security gateway filters will be looking for identical or similar messages from a single source,” says Davey Winder, Security Columnist, “so they won’t detect a longline attack, the messages of which have widely differing subject lines, content and, most importantly, originating IP addresses.”[2]
The chief defense against longline phishing is regular staff training. Regular training can increase vigilance in the workplace and reduce successful attacks. Security controls are also an essential part of an overall plan. Proofpoint also recommends, leveraging “big data systems to analyze email traffic patterns and characteristics on a per-email-recipent level, and would also use URL redirection combined with cloud-based reputation, sandboxing, and other technologies to unify all knowledge about destination URLS and then (when links are clicked) would allow or deny access on a per-URL basis, at clicktime, every time.”
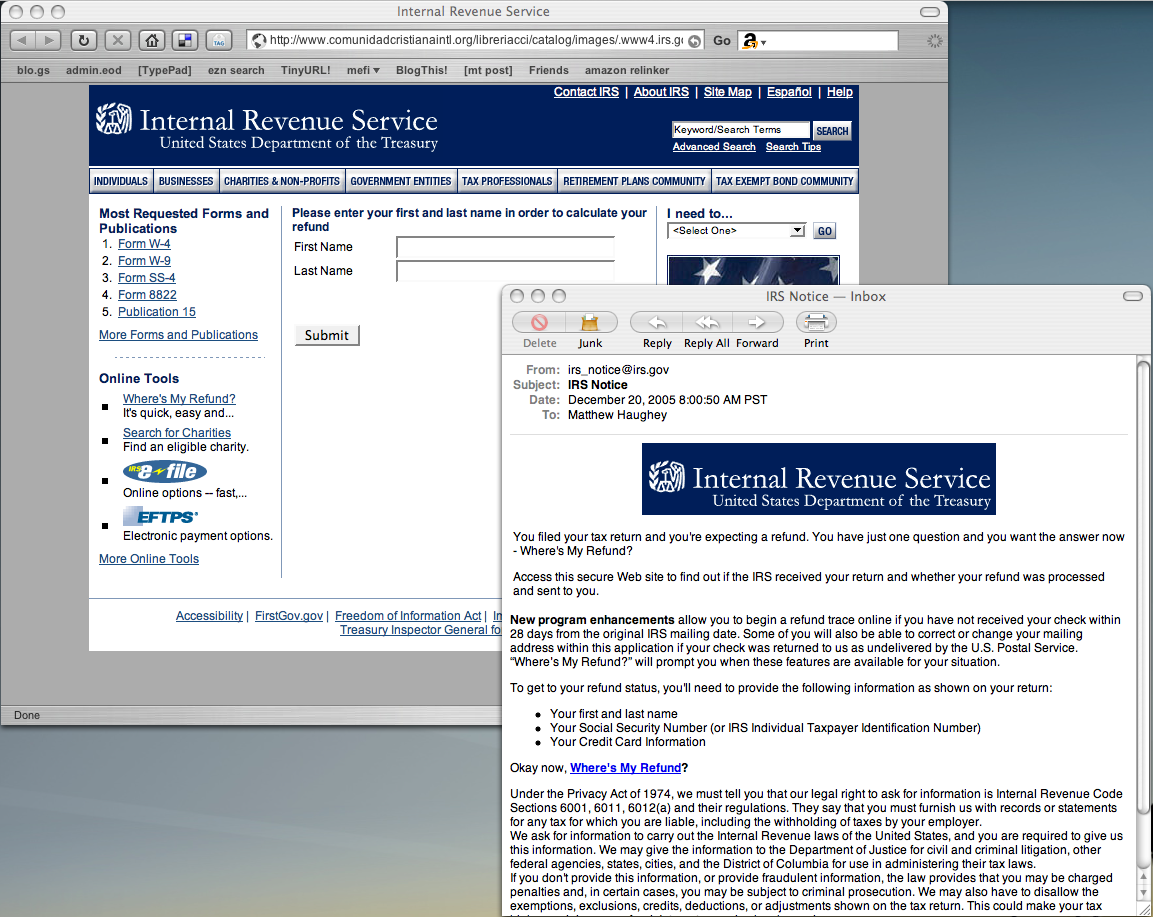
Image used by Creative Commons Permission (by mathowie).
[1] “Longline Phishing: Email-borne Threats, Cloud Computing, Big Data, and the Rise of Industrial Phishing Attacks.” Proofpoint Inc., 2012.
[2] Read more: Longlining: the new phishing attack targeting businesses, PC Pro <http://www.pcpro.co.uk/realworld/382864/longlining-the-new-phishing-attack-targeting-businesses#ixzz2t4NtFBp3″>